
Description
Use-after-free The vulnerability allows a remote attacker to compromise a vulnerable system. The vulnerability exists due to a use-after-free error within the V8 engine. A remote attacker can create a specially crafted web page, trick the victim into visiting it, trigger a use-after-free error and execute arbitrary code on the target system. Successful exploitation of the vulnerability may allow an attacker to compromise a vulnerable system. Note, the vulnerability is being actively exploited in the wild.
Software: Google Chrome

CVSS 2
4.3
Base score
8.6
Exploitability Score
2.9
Impact Score
CVSS 3.1
6.5
Base score
2.8
Exploitability Score
3.6
Impact Score
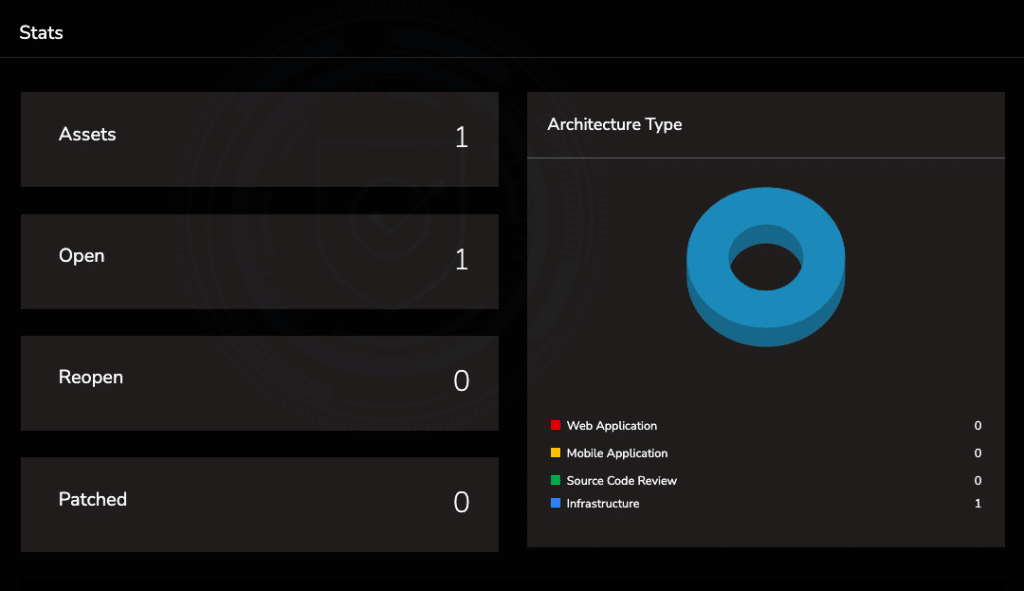
Assets on ESOF by TAC Security
ESOF Vulnerability Management Platforms auto-scans the assets vulnerable to the latest vulnerabilities. It also bifurcates the vulnerable assets by their architecture type, a number of counts of vulnerabilities, assets vulnerable, status; Open, Reopen, Patched all together in one single vulnerability management platform.
Multiple vulnerabilities in Google Chrome
CVE-ID : CVE-2021-37976
Published Date : 30th Sep 2021
Patched Date : 30th Sep 2021
You can request a demo of ESOF VMP to manage the entire IT Stack in one single platform with risk-based vulnerability management.





